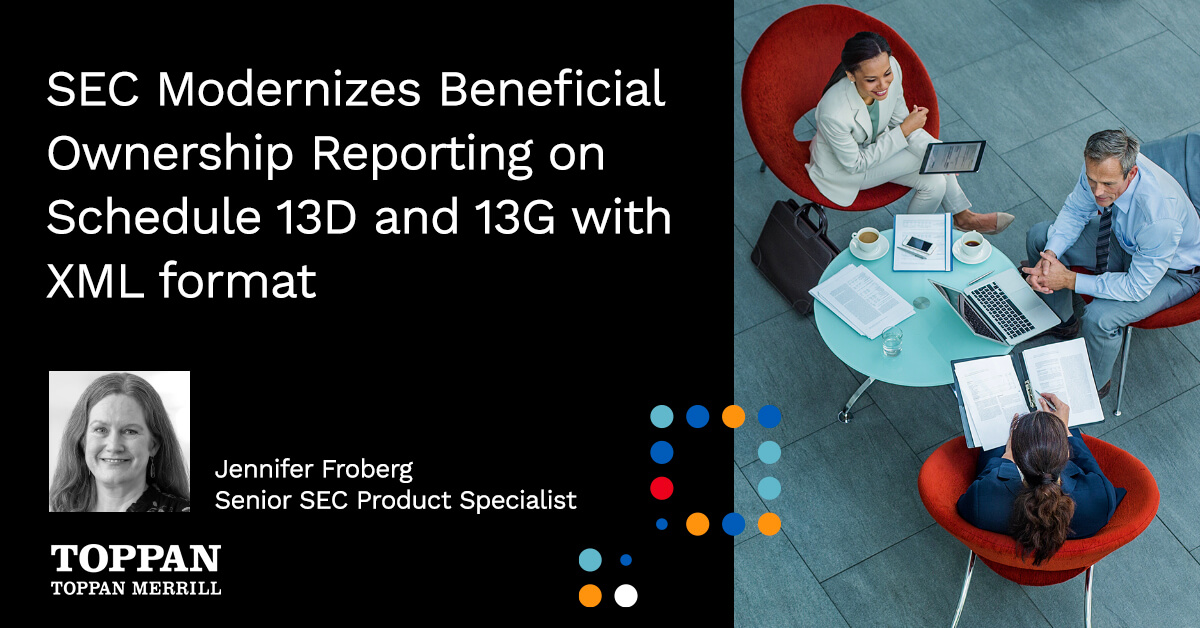
SEC Modernizes Beneficial Ownership Reporting on Schedule 13D and 13G with XML format
Our Toppan Merrill experts break down the SEC’s final rule to update beneficial ownership reporting for Schedule 13D and 13G...
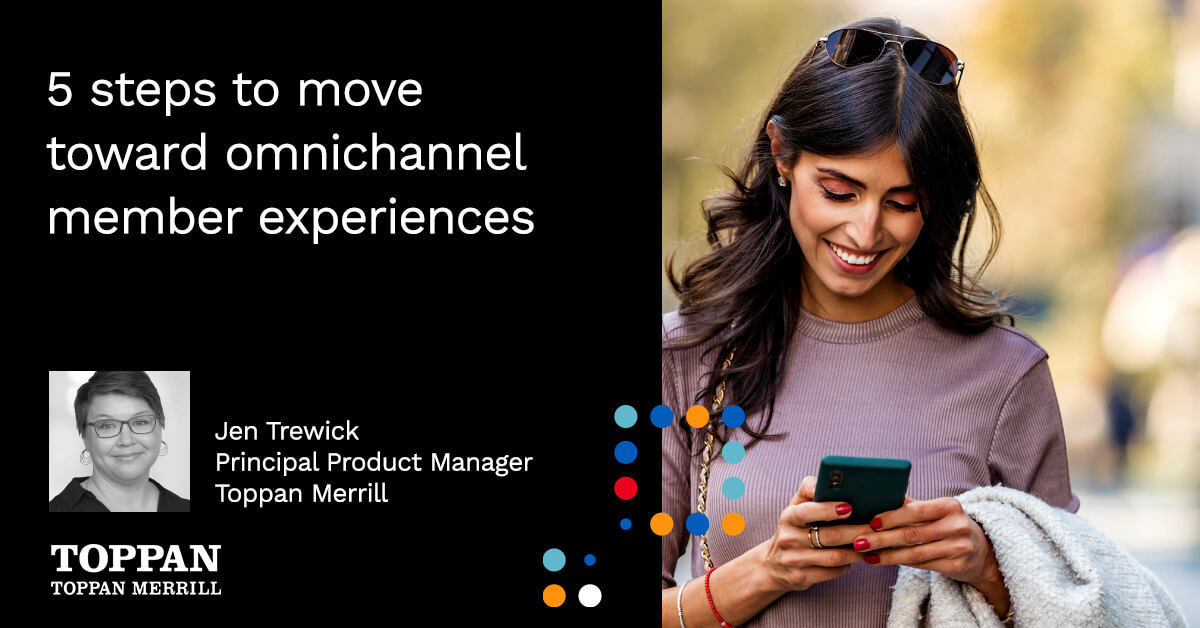
A conversation with Guy Stanzione about the SEC Tailored Shareholder Reports mandate and tackling the data and content management challenges at the share class level.